Security and Privacy in the World-Sized Web
with Berkman Fellow, Bruce Schneier
Tuesday, February 16, 2016 at 12:00 pm
Harvard Law School Campus
Wasserstein Hall, Room B010 Singer Classroom (lower level)
We've created a world where information technology permeates our economies, social interactions, and intimate selves. The combination of mobile, cloud computing, the Internet Things, persistent computing, and autonomy are resulting in something different. This World-Sized Web promises great benefits, but is also vulnerable to a host of new threats. Threats from users, criminals, corporations, and governments. Threats that can now result in physical damage and even death. This talk looks back at what we've learned from past attempts to secure these systems, and forward at what technologies, laws, regulations, economic incentives, and social norms we need to secure them in the future.
About Bruce
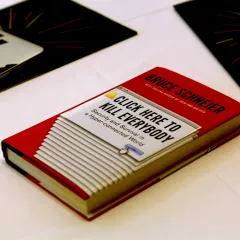
Bruce Schneier is an internationally renowned security technologist, called a "security guru" by The Economist. He is the author of 12 books -- including the New York Times best-seller "Data and Goliath: The Hidden Battles to Collect Your Data and Control Your World" -- as well as hundreds of articles, essays, and academic papers. His influential newsletter "Crypto-Gram" and blog "Schneier on Security" are read by over 250,000 people. Schneier is a fellow at the Berkman Center for Internet and Society at Harvard University, a board member of the Electronic Frontier Foundation, and an Advisory Board member of the Electronic Privacy Information Center. He is also the Chief Technology Officer of Resilient Systems, Inc.
Links
About the Privacy Series
In the fall of 2015, the Berkman Center decided to further surface and highlight our work ongoing work on privacy through the launch of a Berkman Privacy Series, a collection of talks, papers, and other activities, both current and past, that seek to explore and address the increasing concerns about Big Data, which have focused national and international attention on questions of online privacy. Not all of our privacy work is collected in this list, but our hope is that this limited selection, including the future events listed, will serve to increase awareness, foster discussion, and help explore alternative mechanisms for balancing user privacy with the potential benefits of Big Data.
Download original audio or video from this event.
Subscribe to the Berkman Klein events series podcast.