Cybersecurity Project: Difference between revisions
No edit summary |
Rnagarajan (talk | contribs) (Ramesh's final project edits) |
||
| Line 10: | Line 10: | ||
We discussed this topic at length in an in-class presentation on January 19. [http://www.vimeo.com/9036735 This] 9-minute video summarizes and extends the presentation we gave that day. The details on this page elaborate on the proposals mentioned in the video. | We discussed this topic at length in an in-class presentation on January 19. [http://www.vimeo.com/9036735 This] 9-minute video summarizes and extends the presentation we gave that day. The details on this page elaborate on the proposals mentioned in the video. | ||
==Guiding Principles== | |||
Before turning to the specific proposals we've made to improve cybersecurity, it's helpful to discuss some of the guiding principles that have informed our work. We applaud the [http://www.whitehouse.gov/assets/documents/Cyberspace_Policy_Review_final.pdf government's] attempts to improve cybersecurity, but don't believe that a top-down, regulatory or legislative solution is a panacea. | |||
====Empowering Users==== | |||
Cybersecurity is a huge, complicated problem, conceivably including everything from keeping the electrical grid from going down to garden-variety phishing spam. We consciously left the [http://www.sandia.gov/scada/history.htm SCADA] problem to those in government and industry, and focused on problems that face ordinary users. | |||
We suggest tools that rely both on the power users who have contributed much to the internet's development as well as the ordinary users who are the overwhelming share of people online today. Bottom-up solutions seem improbable when they begin; Wikipedia and Firefox, to take just two examples, were thought to face extremely long odds. We believe that giving users the tools they need to take control of their own security can improve users' experiences on the net, as well as convincing major market players to adopt similar solutions that will help everyone, including those users who haven't taken affirmative steps to protect their security. | |||
====Nudging Users==== | |||
The mind sciences and behavioral economics have demonstrated the tinkering with default settings and gently [http://www.nudges.org/ nudging] people in a direction can cause dramatic changes in behavior. We apply that insight to cybersecurity. If it's a little harder to reuse or create weak passwords, or a little easier to find out what malware has infected your computer, security may greatly improve. | |||
====Code is Law==== | |||
[http://en.wikipedia.org/wiki/Lawrence_Lessig Lawrence Lessig's] 1999 insight that [http://www.code-is-law.org/ code is law] is still crucial to understand cybersecurity more than ten years later. Most fundamentally, the major browsers and websites can improve (or worsen) security for users, perhaps much more than the government can. Key browsers and websites, by coding our proposals or other security fixes, can make a major impact on security. | |||
====No big thing, many little things==== | |||
Finally, we consider ourselves [http://berlin.wolf.ox.ac.uk/published_works/rt/HF.pdf foxes, rather than hedgehogs,] and believe that there's no one big thing, or top-down solution, by the government or the private sector, that could solve the cybersecurity problem overnight. Cybersecurity has so many dimensions that it must be improved on all levels, by the government, by industry, by non-profits, and by users. Even if the net suddenly became more secure, in a few months or years new vulnerabilities would be exposed and take the place of the old. As long as the Net remains open, cybersecurity will be a never-ending arms race, and we believe that empowering users, nudging them to better security practices, and remembering that code can be law can give the good guys the upper hand. | |||
==Specific Proposals== | ==Specific Proposals== | ||
| Line 23: | Line 41: | ||
====What is SafeWord?==== | ====What is SafeWord?==== | ||
SafeWord is a real, working FireFox plugin designed to nudge users into keeping safer and more unique passwords, though it's too unstable and unrefined to be considered anything | SafeWord is a real, working FireFox plugin designed to nudge users into keeping safer and more unique passwords, though it's too unstable and unrefined to be considered anything but alpha software at this point. It's available for download [http://www.jasonharrow.com/safeword-1.0.0-fx.xpi here]. To install, save that file to your disk, select File --> Open in Firefox 3.5 or above, and install it. You will need to restart Firefox before it takes effect. Thanks to Elance for helping with the coding on very short notice. | ||
We have created a video demonstration of one of the key features of SafeWord [http://vimeo.com/9031865 here]. | We have created a video demonstration of one of the key features of SafeWord [http://vimeo.com/9031865 here]. | ||
| Line 37: | Line 55: | ||
Even readers who are all for stronger password security in general may nonetheless be skeptical of what can happen to "regular people" who can't be bothered to remember so many passwords. But here's a very scary story - which is taken directly from the [http://www.techcrunch.com/2009/07/19/the-anatomy-of-the-twitter-attack/ Twitter attack analysis] cited above - of what can happen if users employ the same password at multiple important sites: | Even readers who are all for stronger password security in general may nonetheless be skeptical of what can happen to "regular people" who can't be bothered to remember so many passwords. But here's a very scary story - which is taken directly from the [http://www.techcrunch.com/2009/07/19/the-anatomy-of-the-twitter-attack/ Twitter attack analysis] cited above - of what can happen if users employ the same password at multiple important sites: | ||
# HC [the hacker's alias] accessed Gmail for a Twitter employee by using the password recovery feature that sends a reset link to a secondary email. In this case the secondary email was an expired Hotmail account, he simply registered it, clicked the link and reset the password | # HC [the hacker's alias] accessed Gmail for a Twitter employee by using the password recovery feature that sends a reset link to a secondary email. In this case the secondary email was an expired Hotmail account, he simply registered it, clicked the link and reset the password, giving him control of the Gmail account. | ||
# HC then read emails to guess what the original Gmail password was successfully and reset the password so the Twitter employee would not notice the account had changed. | # HC then read emails to guess what the original Gmail password was successfully and reset the password so the Twitter employee would not notice the account had changed. | ||
# HC then used the same password to access the employeeâs Twitter email on Google Apps | # HC then used the same password to access the employeeâs Twitter email on Google Apps, getting access to a gold mine of sensitive company information from emails and, particularly, email attachments. | ||
# HC then used this information along with additional password guesses and resets to take control of other Twitter | # HC then used this information along with additional password guesses and resets to take control of other Twitter employees' personal and work emails. | ||
# HC then used the same username/password combinations and password reset features to access AT&T, MobileMe, Amazon and iTunes, among other services. A security hole in iTunes gave HC access to full credit card information in clear text. HC now also had control of Twitterâs domain names at GoDaddy. | # HC then used the same username/password combinations and password reset features to access AT&T, MobileMe, Amazon and iTunes, among other services. A security hole in iTunes gave HC access to full credit card information in clear text. HC now also had control of Twitterâs domain names at GoDaddy. | ||
# Even at this point, Twitter had absolutely no idea they had been compromised. | # Even at this point, Twitter had absolutely no idea they had been compromised. | ||
| Line 46: | Line 64: | ||
That's the danger, and it ain't pretty. | That's the danger, and it ain't pretty. | ||
On the other hand, we admit | On the other hand, as SafeWord users, we admit that the aspect of the program that requires you to use a different password for each new login is, well, pretty damn annoying. Complying with its demands to keep generating unique passwords might even require some old-fashioned tricks, like the creation of a heuristic for generating memorable but unique passwords or keeping a card in your wallet to keep track of your various logins (and maybe even separating out parts of ''that'' list or keeping it encoded somehow). Still, we think that the cost/benefit analysis weighs in favor of life being just a little more annoying in this area, because as our scary story illustrates, there are '''lots''' of points-of-entry to our various accounts, and '''lots''' of random people out there who would love to hack those accounts for financial gain or to get their kicks. | ||
=====Why Do It This Way?===== | =====Why Do It This Way?===== | ||
| Line 54: | Line 72: | ||
=====Extension v. Built-in Feature===== | =====Extension v. Built-in Feature===== | ||
Initially, we hoped to build this extension to make a pitch to Mozilla that they should think about building this kind of functionality into the browser. But as we have used a now-working copy of SafeWord in our browsers - admittedly, it's an alpha copy that's not even close to ready for prime-time - at least | Initially, we hoped to build this extension to make a pitch to Mozilla that they should think about building this kind of functionality into the browser. But as we have used a now-working copy of SafeWord in our browsers - admittedly, it's an alpha copy that's not even close to ready for prime-time - at least two of us (i.e. jharrow and rnagarajan) see that it's just too intrusive for mainstream users. If the average, busy user gets a pop-up every time he comes across a new website and tries to use an old password, he will get angry at the browser. If this happens a few times, he will probably switch from Firefox to another browser. So right now, the idea works best as an extension for people who really believe in password security and want a little nudge when they are thinking of giving in to the instinct to just use the password they used last time. But if SafeWord could work only with websites that store important personal information -- email providers, financial institutions, retailers with your credit card information -- and ignore the local newspaper's website, perhaps the balance between security and frustration would be a little closer to the former. | ||
====More on the Stronger Password Feature==== | ====More on the Stronger Password Feature==== | ||
Revision as of 19:25, 29 January 2010
Topic Owners: Mike, Jason, Ramesh, and Sheel
Saying that cybersecurity is a "difficult problem" is like saying that reversing global warming is a difficult problem: it's true, but it doesn't quite capture how devilishly complicated and multifaceted the problem really is. There's no single reason why creating a more secure global network is so difficult; it in part has to do with the radically-distributed architecture of the Net, in part with some deep flaws computer software for both consumers and businesses, and in part from the network's sheer size and importance to our daily lives. (For more on this, see the nice Cybersecurity backgrounder.)
Our group approached the problem not with the goal of inventing a panacea that would make all credit card transactions magically secure and make it impossible for hackers to compromise Gmail's security. Instead, we wanted to offer suggestions with minimal implementation headaches and maximal benefit to users, from novices to experts.
The final "product" of our month-long thinking on this issue begins with a reasonably short video overview of our ideas here, (or see below), explains some of the details of our proposal, and also has an alpha-release Firefox plugin that you can download and try out (thanks to Elance for making the plugin possible, by the way).
Overview
We discussed this topic at length in an in-class presentation on January 19. This 9-minute video summarizes and extends the presentation we gave that day. The details on this page elaborate on the proposals mentioned in the video.
Guiding Principles
Before turning to the specific proposals we've made to improve cybersecurity, it's helpful to discuss some of the guiding principles that have informed our work. We applaud the government's attempts to improve cybersecurity, but don't believe that a top-down, regulatory or legislative solution is a panacea.
Empowering Users
Cybersecurity is a huge, complicated problem, conceivably including everything from keeping the electrical grid from going down to garden-variety phishing spam. We consciously left the SCADA problem to those in government and industry, and focused on problems that face ordinary users.
We suggest tools that rely both on the power users who have contributed much to the internet's development as well as the ordinary users who are the overwhelming share of people online today. Bottom-up solutions seem improbable when they begin; Wikipedia and Firefox, to take just two examples, were thought to face extremely long odds. We believe that giving users the tools they need to take control of their own security can improve users' experiences on the net, as well as convincing major market players to adopt similar solutions that will help everyone, including those users who haven't taken affirmative steps to protect their security.
Nudging Users
The mind sciences and behavioral economics have demonstrated the tinkering with default settings and gently nudging people in a direction can cause dramatic changes in behavior. We apply that insight to cybersecurity. If it's a little harder to reuse or create weak passwords, or a little easier to find out what malware has infected your computer, security may greatly improve.
Code is Law
Lawrence Lessig's 1999 insight that code is law is still crucial to understand cybersecurity more than ten years later. Most fundamentally, the major browsers and websites can improve (or worsen) security for users, perhaps much more than the government can. Key browsers and websites, by coding our proposals or other security fixes, can make a major impact on security.
No big thing, many little things
Finally, we consider ourselves foxes, rather than hedgehogs, and believe that there's no one big thing, or top-down solution, by the government or the private sector, that could solve the cybersecurity problem overnight. Cybersecurity has so many dimensions that it must be improved on all levels, by the government, by industry, by non-profits, and by users. Even if the net suddenly became more secure, in a few months or years new vulnerabilities would be exposed and take the place of the old. As long as the Net remains open, cybersecurity will be a never-ending arms race, and we believe that empowering users, nudging them to better security practices, and remembering that code can be law can give the good guys the upper hand.
Specific Proposals
Public Service Announcement
We created a Public Service Announcement for generating public awareness for the cybersecurity problem, and showed it in class on January 19. It's online here but is password-protected. Please email us if you were in the class and would like the password.
The upshot of the video is that we don't think a direct public awareness campaign will be very effective. We believe it would be more productive to nudge users and change their behavior by altering the way browsers and websites work, not by scolding people in 30-second TV ads.
SafeWord
What is SafeWord?
SafeWord is a real, working FireFox plugin designed to nudge users into keeping safer and more unique passwords, though it's too unstable and unrefined to be considered anything but alpha software at this point. It's available for download here. To install, save that file to your disk, select File --> Open in Firefox 3.5 or above, and install it. You will need to restart Firefox before it takes effect. Thanks to Elance for helping with the coding on very short notice.
We have created a video demonstration of one of the key features of SafeWord here.
What Are The Goals of SafeWord?
SafeWord begins with a simple proposition: online passwords should be both strong and also different across different sites, and your browser should help you achieve that goal. Studies continue to show that most people use very simple passwords; see, for instance, this New York Times article that gets right to the point. "If your password is 123456," reads the headline, "just make it HackMe." Moreover, most users also fall into the "dirty habit" of using the same password across multiple online accounts, which can lead to a disaster if only one of the accounts is able to be compromised. An extremely detailed analysis of a 2009 attack that used this principle to compromise many online accounts of Twitter employee is here.
More on The Unique Password Feature
A Scary Story, and A Word About Annoyance
Even readers who are all for stronger password security in general may nonetheless be skeptical of what can happen to "regular people" who can't be bothered to remember so many passwords. But here's a very scary story - which is taken directly from the Twitter attack analysis cited above - of what can happen if users employ the same password at multiple important sites:
- HC [the hacker's alias] accessed Gmail for a Twitter employee by using the password recovery feature that sends a reset link to a secondary email. In this case the secondary email was an expired Hotmail account, he simply registered it, clicked the link and reset the password, giving him control of the Gmail account.
- HC then read emails to guess what the original Gmail password was successfully and reset the password so the Twitter employee would not notice the account had changed.
- HC then used the same password to access the employeeâs Twitter email on Google Apps, getting access to a gold mine of sensitive company information from emails and, particularly, email attachments.
- HC then used this information along with additional password guesses and resets to take control of other Twitter employees' personal and work emails.
- HC then used the same username/password combinations and password reset features to access AT&T, MobileMe, Amazon and iTunes, among other services. A security hole in iTunes gave HC access to full credit card information in clear text. HC now also had control of Twitterâs domain names at GoDaddy.
- Even at this point, Twitter had absolutely no idea they had been compromised.
That's the danger, and it ain't pretty.
On the other hand, as SafeWord users, we admit that the aspect of the program that requires you to use a different password for each new login is, well, pretty damn annoying. Complying with its demands to keep generating unique passwords might even require some old-fashioned tricks, like the creation of a heuristic for generating memorable but unique passwords or keeping a card in your wallet to keep track of your various logins (and maybe even separating out parts of that list or keeping it encoded somehow). Still, we think that the cost/benefit analysis weighs in favor of life being just a little more annoying in this area, because as our scary story illustrates, there are lots of points-of-entry to our various accounts, and lots of random people out there who would love to hack those accounts for financial gain or to get their kicks.
Why Do It This Way?
There are other solutions out there that automatically generate secure, unique passwords for each site you visit; LastPass is a particularly nifty one. But they all share several key points of failure: they rely on a master password, and they store your passwords in the cloud. Relying on a master password is particularly problematic, because a compromise of that password can lead to the same disastrous chain of events that we are trying to prevent. The only way to truly reduce the risk of this type of threat is to decentralize everything. And if that takes encouraging people to work a little harder, we at least want to make people aware that this just might be worth the hassle. Similarly, there are problems with storing passwords in the cloud, including intruder problems and problems if the company goes out of business or the cloud becomes inaccessible.
Extension v. Built-in Feature
Initially, we hoped to build this extension to make a pitch to Mozilla that they should think about building this kind of functionality into the browser. But as we have used a now-working copy of SafeWord in our browsers - admittedly, it's an alpha copy that's not even close to ready for prime-time - at least two of us (i.e. jharrow and rnagarajan) see that it's just too intrusive for mainstream users. If the average, busy user gets a pop-up every time he comes across a new website and tries to use an old password, he will get angry at the browser. If this happens a few times, he will probably switch from Firefox to another browser. So right now, the idea works best as an extension for people who really believe in password security and want a little nudge when they are thinking of giving in to the instinct to just use the password they used last time. But if SafeWord could work only with websites that store important personal information -- email providers, financial institutions, retailers with your credit card information -- and ignore the local newspaper's website, perhaps the balance between security and frustration would be a little closer to the former.
More on the Stronger Password Feature
On the other hand, the idea of adding a feature that helps users create more secure passwords - even if they are reused across multiple accounts - is a simple fix that should enhance the browsing experience for most users.
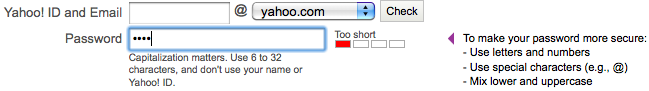
Increasingly, many websites are giving users some guidelines on password security. For instance, Yahoo!'s sign-up page looks like this:
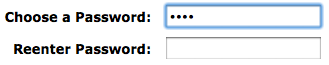
We think that's great. But not all sites have that feature. For instance, you get no visual feedback if you sign-up for an Amazon account with a weak password:
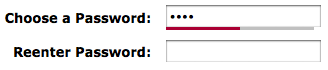
Your browser can change this state-of-affairs easily. Here's the new view, with a SafeWord bar underneath the password field reminding you that your password is weak:
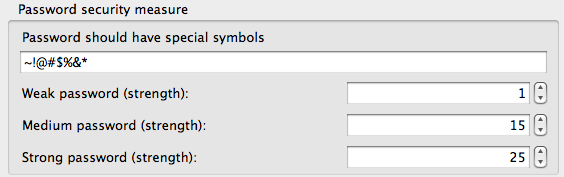
SafeWord even lets you customize the password strength options:
We think something like this really could be built into the browser, and would both add to the user experience and increase security.
"Amber Alert" For The Internet
Even if websites invest a lot of time and effort into securing their servers and user data, few sites take a more systematic approach to cybersecurity and view the massive numbers of compromised user machines as as "their" problem; they don't have any ownership over the fact that so many computers are running nasty malware and are thus compromised in important ways that can cause systemic harm to the Internet (like, say, when a site is taken offline in a Distributed Denial-of-Service attack; a partial list of such incidents is here). However, there are some promising signs this may be changing.
Perhaps these initiatives can go even further. What if a coalition of leading Internet sites were willing to share certain information about security threats with a third party organization (like StopBadware), and the third-party would vet the information and then issue certain "Amber Alerts" that all the sites would be willing to publicize in some way? When there's a particularly egregious security hole in an old browser, for instance, if all the leading websites actively encouraged its users to patch it, that has the potential to do a lot of good.
We initially proposed this solution as a unilateral move that individual sites could make - Google, say, could warn its users about the vulnerabilities of Internet Explorer 6. But we've realize that if the recommendations are filtered through a reliable third-party, perhaps the companies won't be threatened by the embarrassment of having an "Amber Alert" put out. Sure, there would be negative consequences for a company, just as a company who undertakes a product recall generates bad publicity. But ultimate the hope is that companies will realize the net positive value of this transaction, and that consumers will look kindly on companies promoting a new level of honesty and transparency.
Good Cyber-Samaritans
An idea we discussed on January 19 that was related to the "Amber Alert" system for websites involves empowering educated users to help out their less computer-savvy friends and neighbors with computer security problems just...because. Perhaps there could be a network of young people who think security is important and who don't mind hanging around their local library for a few hours helping people update software and patching security holes. This solution becomes ever-more feasible as a greater proportion of users switches to laptop computers and as projects showing that people are willing to assist strangers for the sheer fun and satisfaction of the experience - from building an encyclopedia to giving them a couch to crash on for free - flourish. Relying on people's good natures could be a new way to make progress on this problem.